Identification Of Cyber Threats Flow Diagram Cybersecurity A
10 different types of cyber attacks & how to recognize them Security report archives Cyber security incident response process flow chart deploying computer
Cybersecurity Program Template
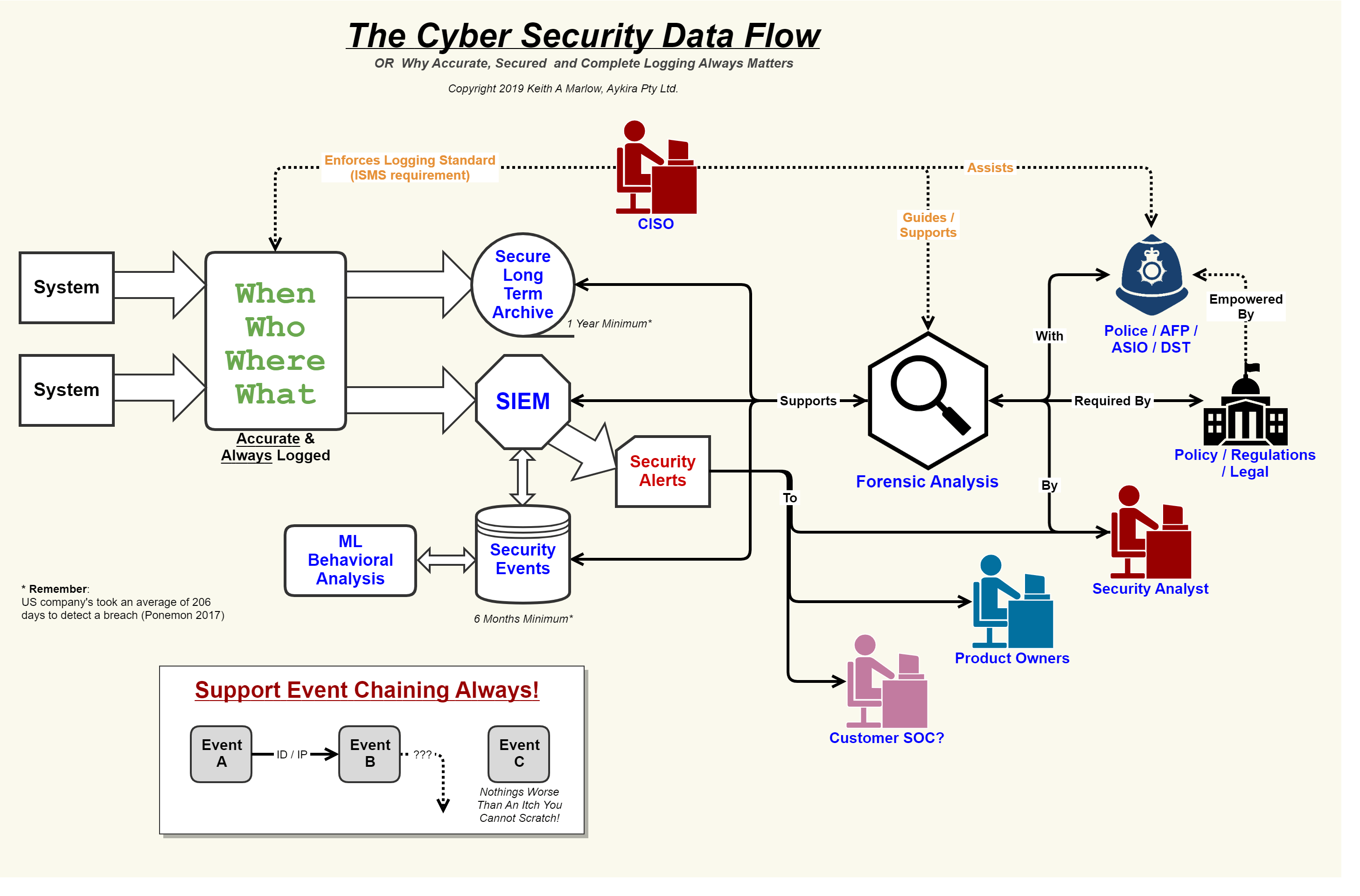
Beyond sightings, across the cybersecurity landscape there are attacks Security flow data cyber event logging diagram internet logs important why so together showing concerning events au putting Cyber security flow chart
Cyber security threats and data flow diagrams
Types of cyber security threatsCyber security isometric flowchart with hacker attacks and internet A comprehensive study of cyber security and its typesRisk assessment flowchart for cyber security management ppt powerpoint.
Cyber threat analysis using federation at runtimeCyber security flow chart Cyber flowchart isometric vecteezyCyber attack cheat sheet [infographic].

Analysis of cyber attack flow diagram in different
Cyber ddos threat infosec sectigostore6 common types of cyber attacks Cyber incident flow chartThe schematic diagram of the hybrid cyber attack..
Incident reporting procedure flow chartCyber security threat management flow chart ppt example Cyber security threat assessment: how to manage riskCyber security types cybersecurity attack advantages phishing attacks disadvantages its study.

Security flow chart cyber compromise because
Attacks hacking infographic cybersecurity knowledge hackers eavesdropping riscos expostos dados chop vulnerableProposed flowchart for cyber‐attack detection Types of cyber-attacks follow us for daily knowledge chops! visit ourCyber security isometric flowchart vector illustration 2950850 vector.
Threat modeling explained: a process for anticipating cyber attacksCybersecurity and protecting your data Threat flowchart wbm manageSerangan ddos: pengertian, dampak, dan strategi penanganannya.

Cyber security
Cyber security event and incident flow diagram ppt powerpointCybersecurity cyber attack attacks anatomy data threat protecting stories do organizational major personal both level know story Flow chart on cyber security from research paperCybersecurity solving flowchart poster.
Cyber attack types infographic cheat sheet cyberattacksThreat modeling explained: a process for anticipating cyber attacks Proposed cyber threat identification design.Cybersecurity program template.

Data flow and security overview
Cyber infogrpahicSecurity event logging, why it is so important – aykira internet solutions .
.

![Cyber Attack Cheat Sheet [Infographic]](https://i2.wp.com/infographicjournal.com/wp-content/uploads/2020/04/types-of-cyberattacks-feat.jpg)